Intro
This is my homelab side project that I’ve been working on for the past 3 years. It went through being just an old laptop with a virtualized network to a small server rack that has been helping me put my skills into practice in a small, scalable environment.

Architecture
I put emphasis on secure-by-design architecture, making the network segmented through VLANs to prevent inter-domain ARP spoofing, forcing all inter-domain communications to come through the firewall instead. The network features centralized authentication at multiple points, including 802.1X RADIUS authentication for wireless and VPN clients using Active Directory Domain Controller as an Identity Provider, hardened per CIS guidelines. The network has two Certificate Authorities - one air-gapped and being the root CA for local domain and an intermediate CA on the Domain Controller to issue certificates to Windows hosts and secure RDP connections. All data is encrypted at rest and in transit at all points of the network flow.
The network features a micro-scale SOC solution built on top of Stamus Networks Clear NDR (Formerly SELKS) based on ELK Stack and Suricata, which analyzes all intra- and inter-domain traffic through a SPAN port on the upstream switch for full network visibility and logging of all packets for further analysis and threat hunting activities. All hosts on the network have appropriate audit information collected and shipped to Elasticsearch for enrichment and logging purposes. This had been set up so that I could practice scalable on-prem SOC deployment, connecting the endpoints as well as configuring them for proper telemetry logging, and threat hunting and analysis activities on the deployed solution. This also provides me with holistic visibility of the whole network and helps with troubleshooting and security assessments. This was originally built on a manual ELK Stack deployment with Suricata, Beats and syslog collectors, but has been since rebuilt using Clear NDR as a more streamlined solution.
The inter-domain and VPN traffic is routed through pfSense firewall with a tight least-privilege ACL ruleset. Whenever possible, I’ve avoided using Docker for architecture and software stack deployments and opted for manual configuration instead so that I could learn more.
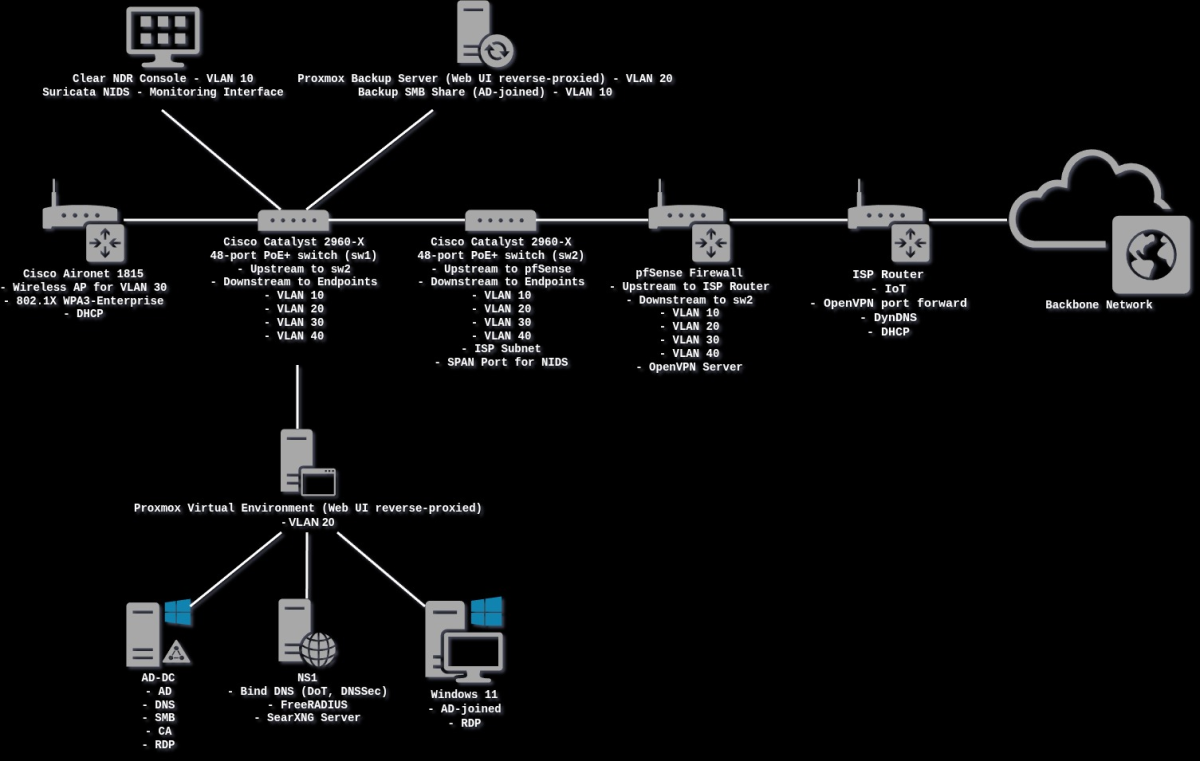
The network is segmented into the following VLANs:
- VLAN 10 (CRITICAL) - SOC console interface and Elastic collectors, backup network shares, Cisco SSH interfaces
- VLAN 20 (SERVERS) - Client-facing and server dependency services - Bind DNS server with full DoT support and direct upstream to root nameservers with no intermediaries for privacy, FreeRADIUS server, AD DC with any SMB shares for clients, Windows 11 Workstation and Server 2025 Domain Controller RDP servers, Proxmox VE management interface, Proxmox Backup Server management interface, SearXNG search server, OpenProject deployment, as well as any other useful services and dashboards
- VLAN 30 (AUTHORIZED) - Authorized clients connecting to the network that should be allowed access to client-facing services (these are configured via firewall ACLs and access to services like SSH and RDP, access to the Critical subnet, etc. are assigned on a per-IP basis), Cisco Wireless Access Point with 802.1X PEAP authentication to provide authorized users with wireless access to the network, DHCP Server, Local LLM hosted outside the server rack on my host as well as any personal SMB shares I use with my personal devices
- VLAN 40 (UNAUTHORIZED) - Unauthorized endpoints (ex. IoT devices, guests at home) - currently unused, as the ISP subnet is used for that purpose, with only egress traffic allowed
- OpenVPN - This subnet is routed as needed, with each client having a forced IP address and being provided with routing to only the required services. Traffic Shaping is incorporated to prioritize packet scheduling of those connections to provide more semless RDP/SSH experience and better network share performance for the clients. Since the server utilises tls-crypt-v2 for instances of clients connecting from a DPI-powered public Access Points, this becomes especially important due to double-encapsulation/double-encryption, and the connections being TCP. The whole network was optimized with the highest non-fragmentable MTU. Client-specific overrides are highly utilised to pin each client certificate’s IP address for the ACLs to work as intended.

Management
I prefer to use SSH for most tasks (I tended to use RDP with the DC, but since I’ve set up Powershell Core over SSH, this has become redundant), but for physical host reboots (all drives are LUKS-encrypted), firmware changes and network connectivity troubleshooting I have a 4-host KVM with keyboard and mouse, and a small display at hand with all cabling coupled in a tunnel next to the rack. The rack has air cooling connected to a 12V thermostat. The Cisco switches utilised are 2960-X 48-port PoE+ models with 10G SFP ports and had horrendously loud cooling, so I replaced it with small quiet Noctua fans i wired myself that are placed in 3D-printed cases.